Facebook BugBounty: Intercept incoming friend requests of Victim add/accept to your facebook account:
Product/URL: Facebook android app on facebook
Description and Impact
The issue:
Missing authorisation check while accessing friend request API on android app, an attacker can add friend requests of any facebook user into his own account.
Missing authorisation check while accessing friend request API on android app, an attacker can add friend requests of any facebook user into his own account.
in simple words Peter says:
Wait, what, no, no, Peter is a nice fellow.
Peter: Ok, but still
Its like I can intercept and accept friend requests from someone
which was send to some other user via Facebook send friend request to contacts
option.
Let's report!!
Sceanrio:
X sends friends request by contacts option to Y.
And I can get the request which was send to Y and become friend
with X.
Reproduction Instructions/Proof of Concept:
1. install latest android app.
2. Create new account.
3. Enter a random mobile number[victim's].
4. Enter a good name.
5. Enter gender.
6. You can skip uploading photo as well as uploading contacts.
7. As soon as you land on fb home page you can go the friend tabs
and can see the friend request that were send to X from Y.
8. You can accept the friend request of Y and Y is your friend.
Impact:
This bypasses fb authentication to
add friends from contact, the valid check to confirm the contact number should
come before landing on the home page. Else one can easily accept friend
requests thus getting their personal details that are actually meant to be
shared with the friends.
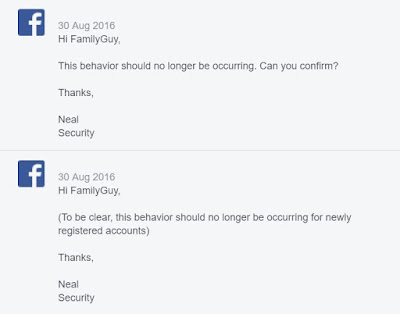
Reported to Facebook: 25th August 2016First reply:
Second reply:
Fix Confirmed:
Mitigation: user was asked to confirm the mobile number, before the friend requests accessibility was allowed.
Bounty Awarded:
Meanwhile Lois:
and me :
Thanks Facebook Security for the quick resolution and an awesome program:
./Family Guy








well, this was scary. You would have known easily who all were stalking girls :D
ReplyDeleteand also having access to the friends only content, am still interested how much facebook paid for !
Nice one, Family Guy :)